Embracing a Zero Trust Security Model
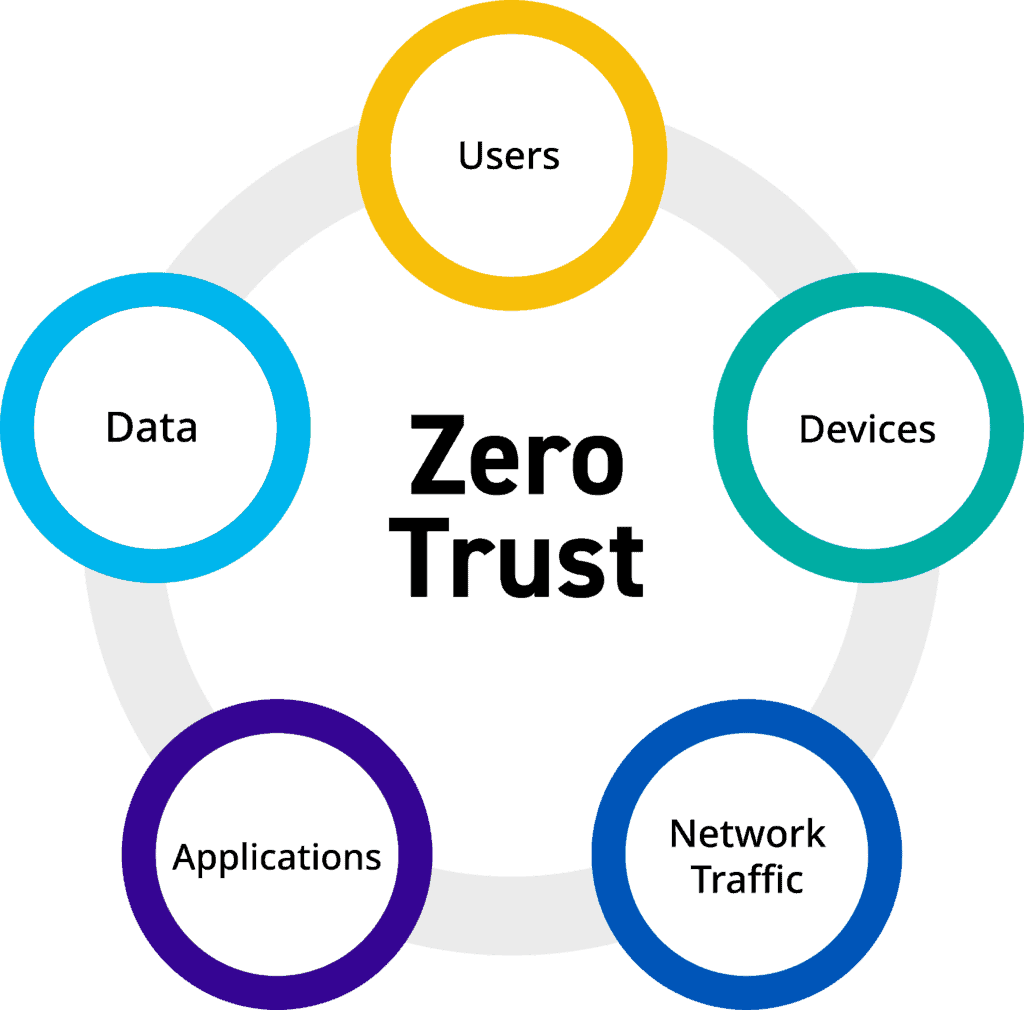
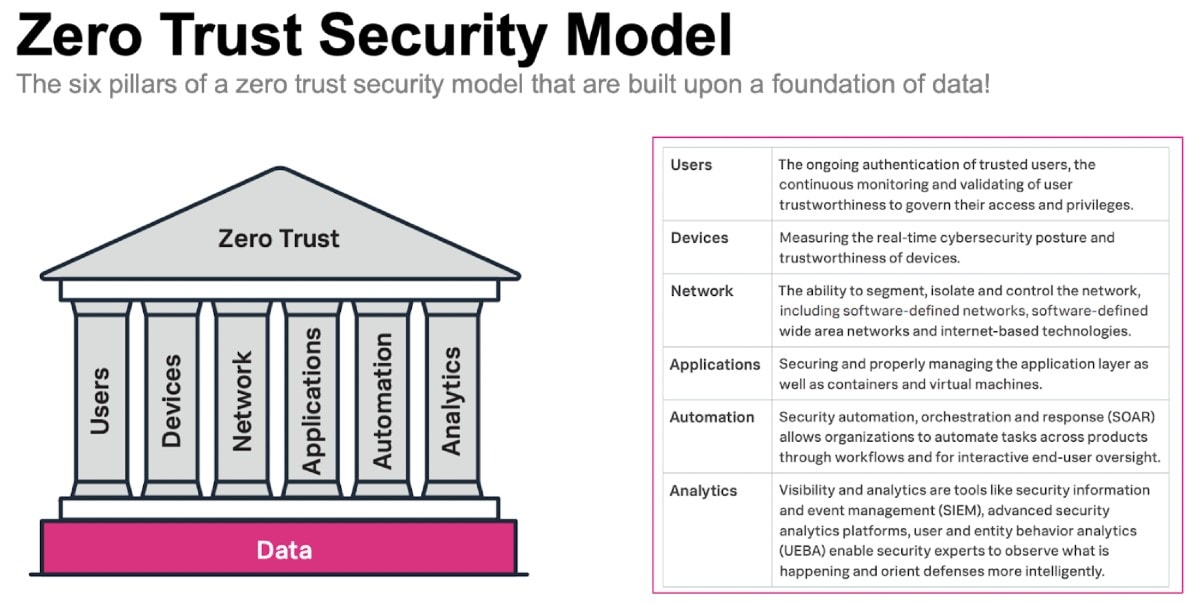
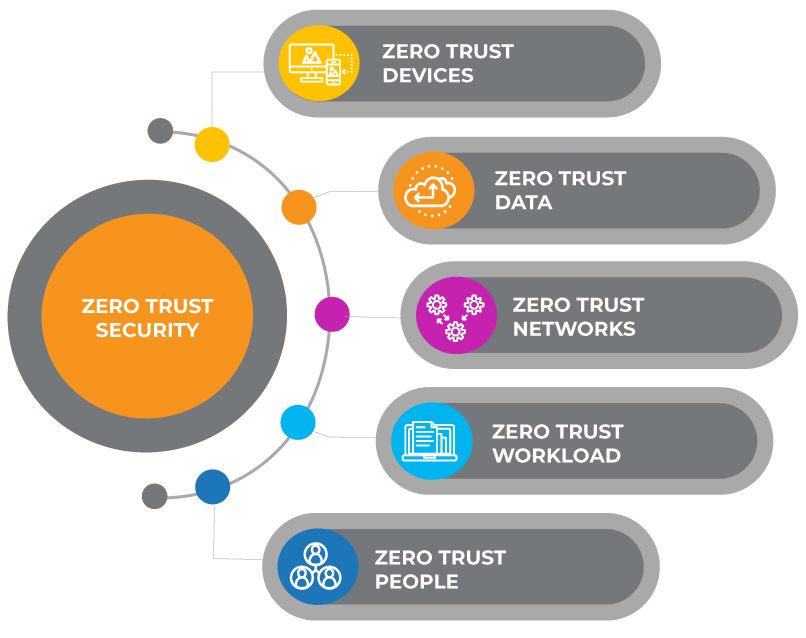
Modern-day organizations require an adaptive and resilient Zero Trust security model to effectively protect people, devices, and data.

Build a Zero Trust Roadmap

Moving Beyond the Buzzword: Embracing Zero Trust Identity

The Vulnerability of Zero Trust: Lessons from the Storm 0558 Hack
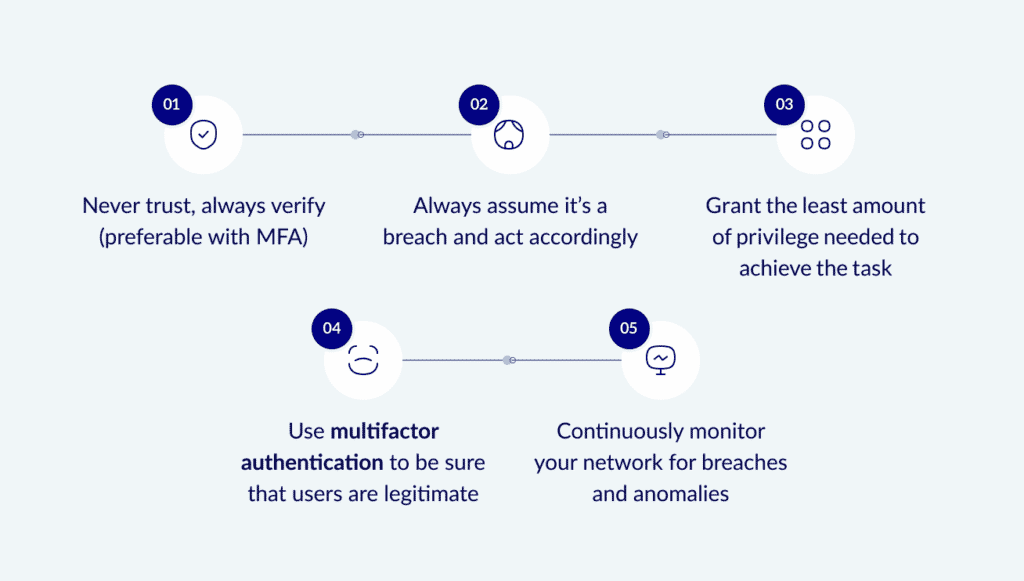
What Is Zero Trust Security? A Practical Guide
A Zero Trust Security Approach for Government: Increasing Security but also Improving IT Decision Making
Cybersecurity Trends You Should Be Watching for 2021 - Edafio

Embracing Zero Trust (Part 4 of 7): Continuous Supply-Chain Risk Awareness

Transitioning from VPNs to Zero Trust Network Access: A Safer Approach
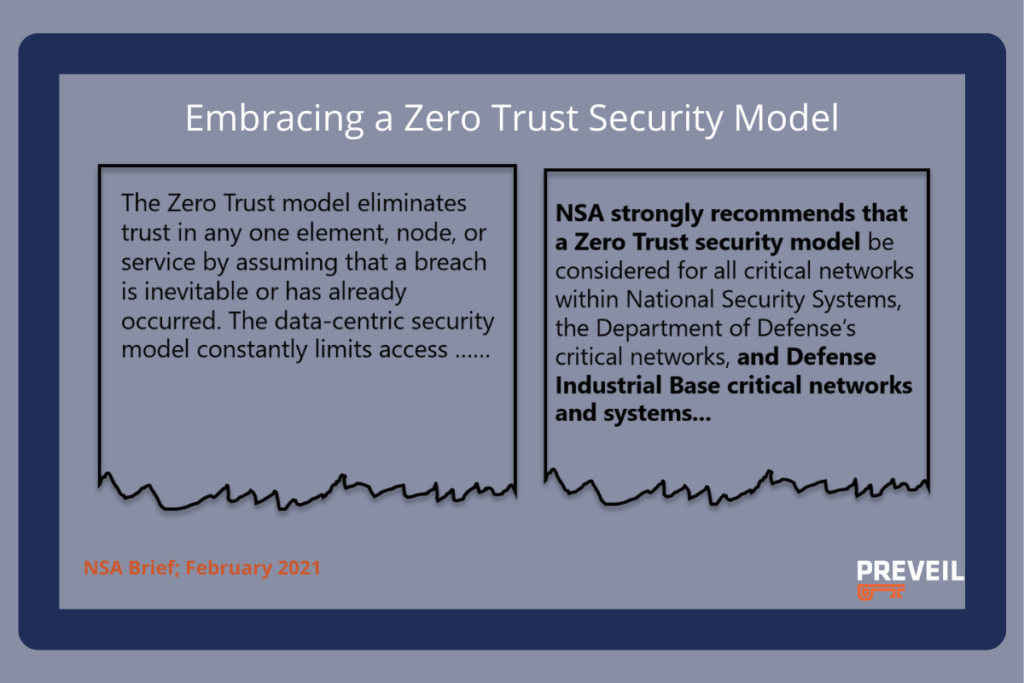
Zero Trust is the Only Way: President Biden's Executive Order Simplified - PreVeil
How to Understand and Implement CISA's Zero Trust Maturity Model - SentinelOne
)
Embracing AI-Powered Security and Zero Trust in a Dynamic Threat Landscape - GovWare

Cybersecurity Speaker Series: Embracing a Zero Trust Mindset > National Security Agency/Central Security Service > Article
4 Cybersecurity Necessities in the Work-From-Anywhere Landscape