What is System Hacking in Ethical Hacking? How to Prevent from It

Know all about what is system hacking in ethical hacking? Explore the comprehensive guide on system hacking prevention, types & processes explained by EC-Council

Ethical Hacking Career in 2024
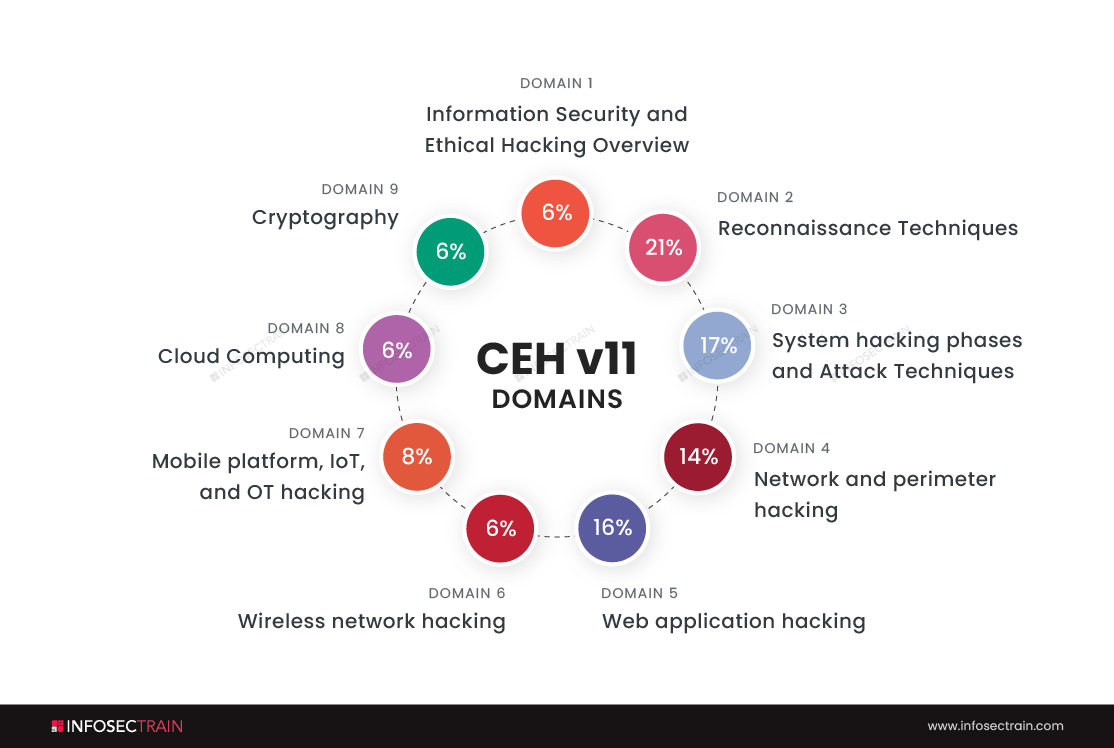
Domain 3 of CEH v11: System Hacking Phases and Attack Techniques

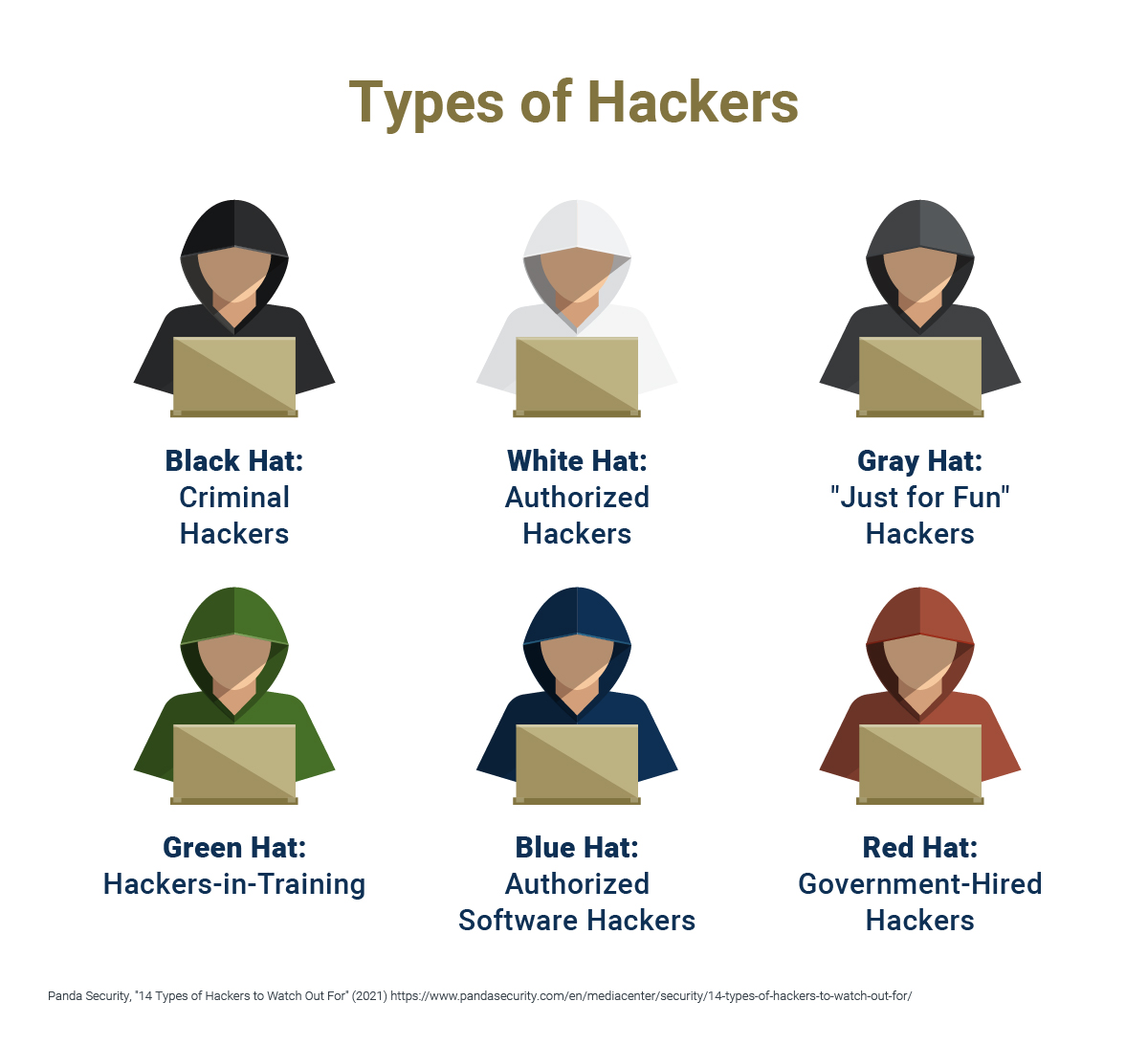
What Is Ethical Hacking?

Phases of Ethical Hacking - InfosecTrain

The Definitive Guide To Ethical Hacking - MyComputerCareer

How Can You Prevent Hacking? Tips To Protect Your Devices
Ethical System Hacking: Access to Execution is the sixth book in the Ethical Hacking series, designed to prepare cybersecurity professionals for

Ethical Hacking Volume 6: Ethical System Hacking: Access to Execution
The Complete Guide to Ethical Hacking

10,336 Prevent Hacking Images, Stock Photos, 3D objects, & Vectors

What is Ethical Hacking & How Does it Work?
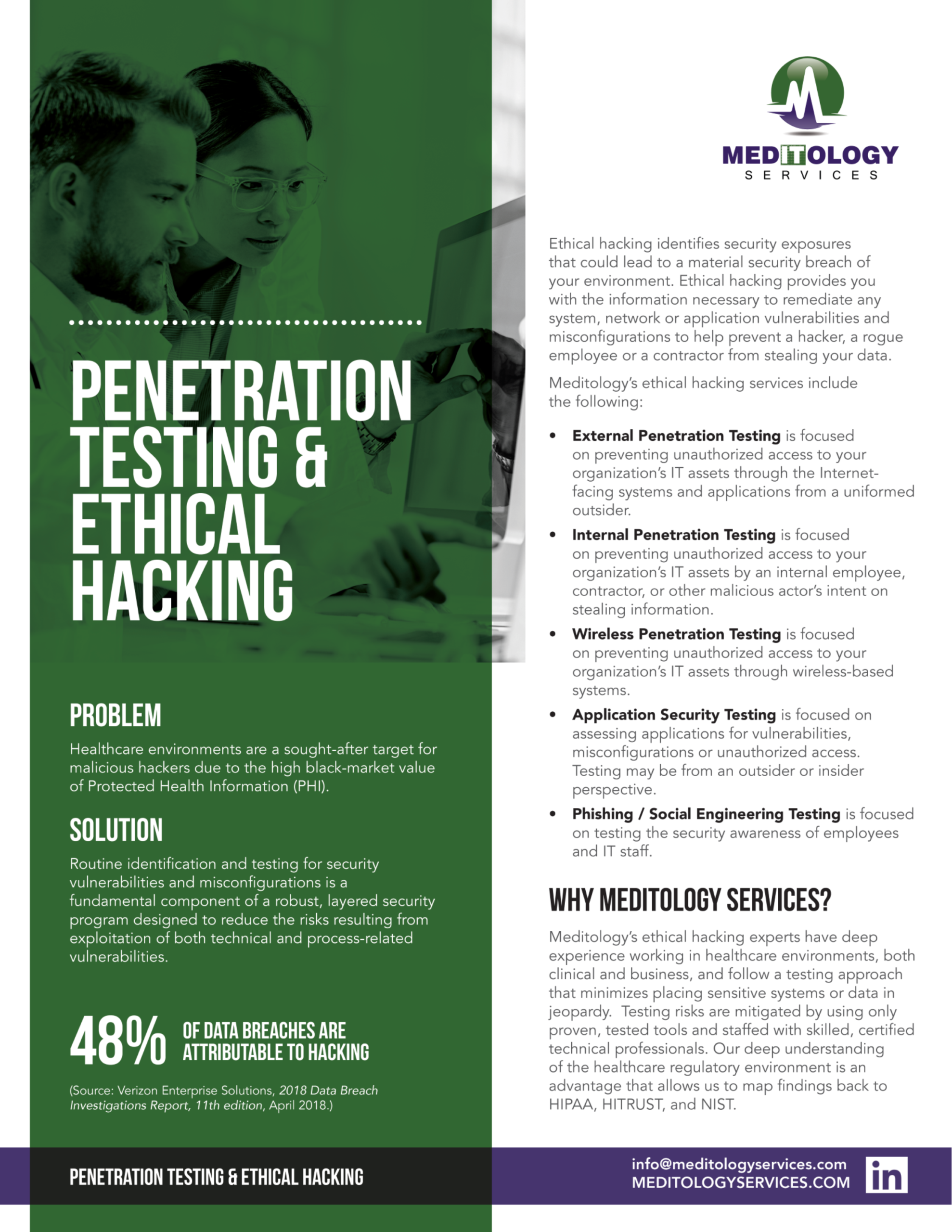
Penetration Testing & Ethical Hacking - Meditology Services

🤵🏻What is Ethical Hacking? How Does it Work?

SOLUTION: System hacking - Studypool

Ethical hacking and social engineering









