Hacking Humanitarians? IHL and the protection of humanitarian organizations against cyber operations – EJIL: Talk!

For some years, experts have cautioned that the more humanitarian organizations collect data, the more they ‘are exposed to a growing wave of digital attacks and cyber espionage, and have become highly prized targets’. In late January 2020, the issue made headlines: The New Humanitarian reported a ‘sophisticated’ cyber operation against the UN, including the […]

Massimo Marelli - Humanitarian Law & Policy Blog

Vincent Cassard (@VCassardICRC) / X

Cyber operations and international humanitarian law: five key points - Humanitarian Law & Policy Blog

Applying International Humanitarian Law to Cyber Warfare, in Law and National Security: Selected Issues, INSS Memo
Full article: Digitisation and Sovereignty in Humanitarian Space: Technologies, Territories and Tensions
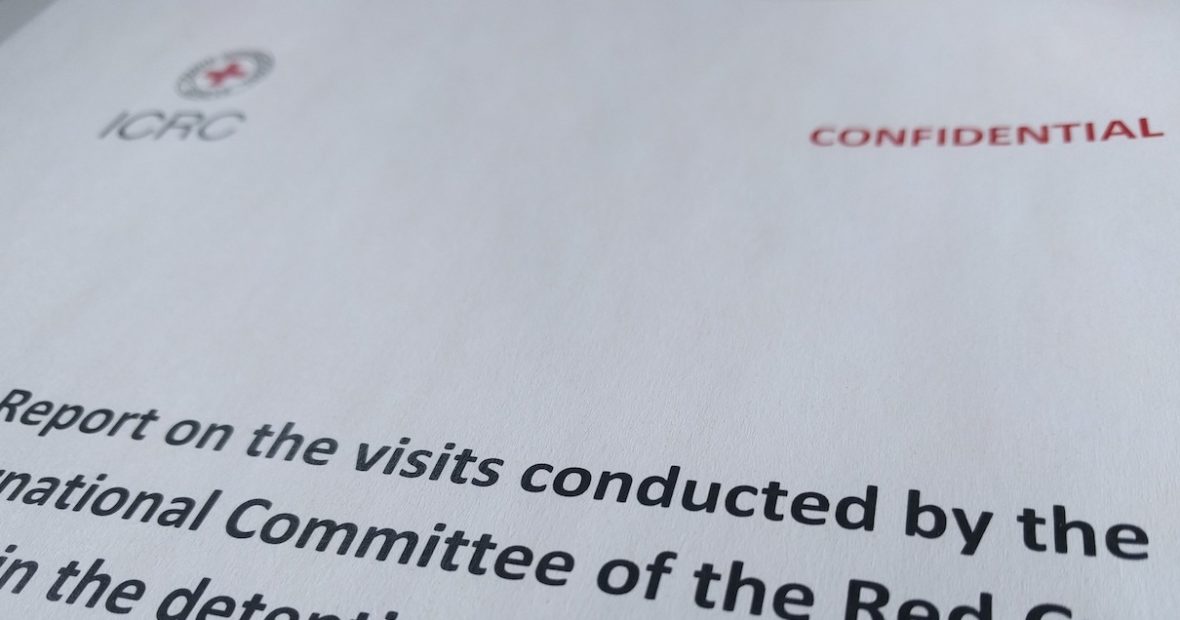
5 things that make ICRC confidential information unsuitable for legal proceedings - Humanitarian Law & Policy Blog

Hacking Humanitarians? IHL and the protection of humanitarian organizations against cyber operations – EJIL: Talk!

Hacking humanitarians: moving towards a humanitarian cybersecurity strategy - Humanitarian Law & Policy Blog

Foghorns of war: IHL and information operations during armed conflict

Hacking humanitarians: operational dialogue and cyberspace - Humanitarian Law & Policy Blog

PDF) CYBERSPACE AND INTERNATIONAL LAW

Scenario 25: Cyber disruption of humanitarian assistance - International cyber law: interactive toolkit

Hacking humanitarians: mapping the cyber environment and threat landscape - Humanitarian Law & Policy Blog

Tilman Rodenhäuser auf LinkedIn: Great to see our blog on 'Safeguarding Humanitarian Organizations from…

Understanding digital risks in armed conflict