Pseudo-Code for Typex Encryption and Stepping

Download Table | Pseudo-Code for Typex Encryption and Stepping from publication: Cryptanalysis of Typex | Rotor cipher machines played a large role in World War II: Germany used Enigma; America created Sigaba; Britain developed Typex. The breaking of Enigma by Polish and (later) British cryptanalysts had an enormous impact on the war. However, despite being based on the | Cryptanalysis, Machines and Wire | ResearchGate, the professional network for scientists.

Encryption technique based on chaotic neural network space shift

Discourse Encrypt (for Private Messages) - plugin - Discourse Meta
Suites: Ciphers, Algorithms and Negotiating Security Settings
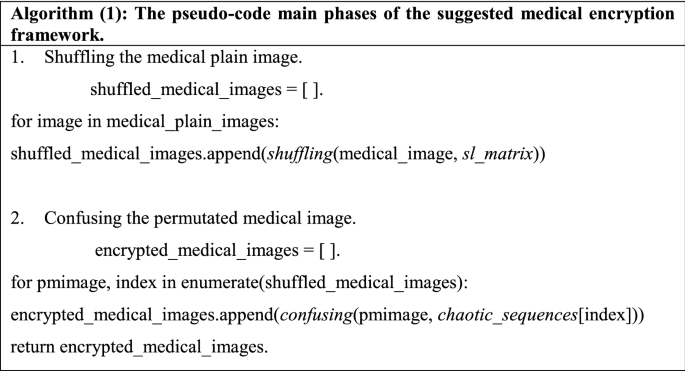
Proposed neural SAE-based medical image cryptography framework

Algorithm A l (pseudocode for a leader robot r i ).
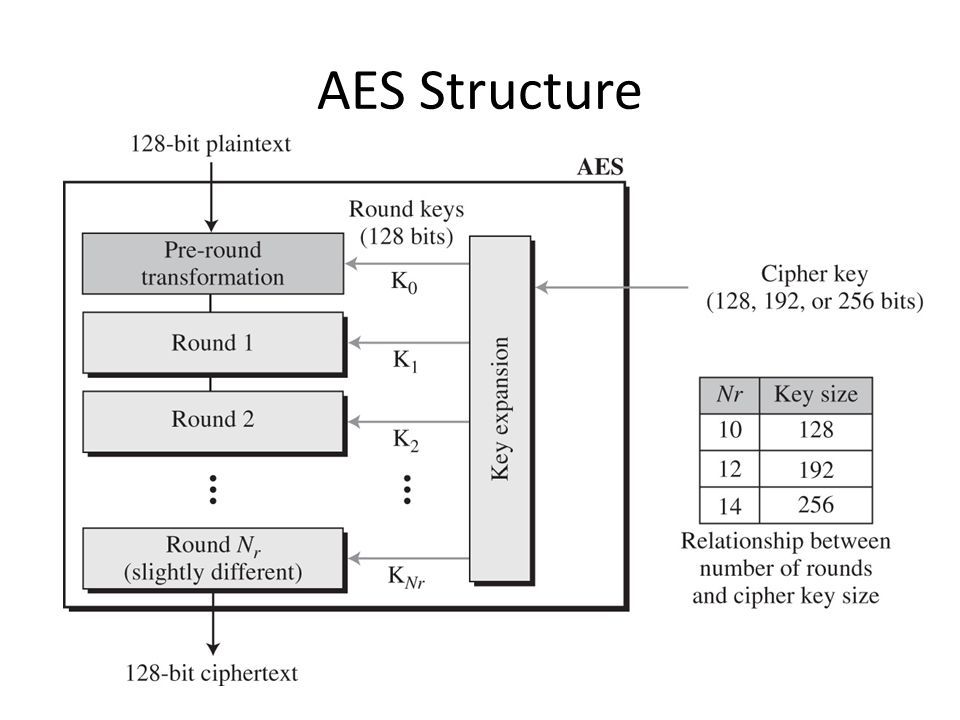
Encryption 101: How to break encryption

How to Build an Encryption Algorithm: 6 Steps

Arnold transform and blockchain based signcryption scheme for

The MSK: a simple and robust image encryption method
Challenging the Security of Logic Locking Schemes in the Era of