PDF] Developing Anti Spyware System using Design Patterns
![PDF] Developing Anti Spyware System using Design Patterns](https://d3i71xaburhd42.cloudfront.net/9af2098e532ff823f058576ae758851a80596e36/4-Table1-1.png)
A framework for anti spyware system that combine data mining and design patterns in detecting and classifying spyware is introduced that can be reusable as it can modify itself for any new or modified spyware. Spyware is considered a great threat to confidentiality since it can cause loss of control over private data for computer users. This kind of threat might select some data and send it to another third party without the consent of the user. Spyware detection has been presented traditionally by three approaches signature based detection, behavior based detection and specification based detection. These approaches were successful in detecting known spyware but have proven failure in detecting unknown spyware. In this paper we introduce a framework for anti spyware system that combine data mining and design patterns in detecting and classifying spyware. The proposed anti spyware system can be reusable as it can modify itself for any new or modified spyware.

The Incredible Rise of North Korea's Hacking Army

The Repressive Power of Artificial Intelligence

Antivirus software - Wikipedia
The Hacked World Order Council on Foreign Relations

Semiconductors and the U.S.-China Innovation Race – Foreign Policy
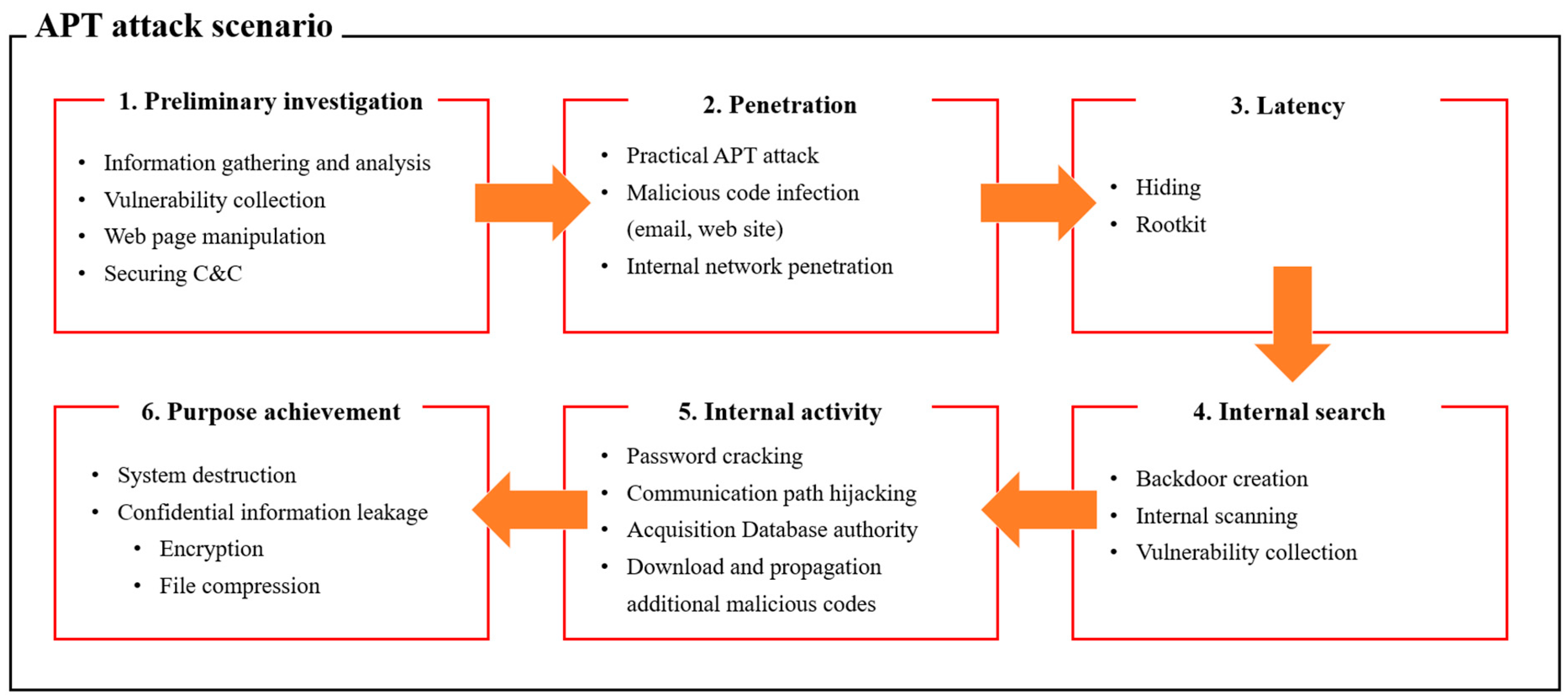
Applied Sciences, Free Full-Text

Kaspersky malware report for Q3 2023

A new deep boosted CNN and ensemble learning based IoT malware
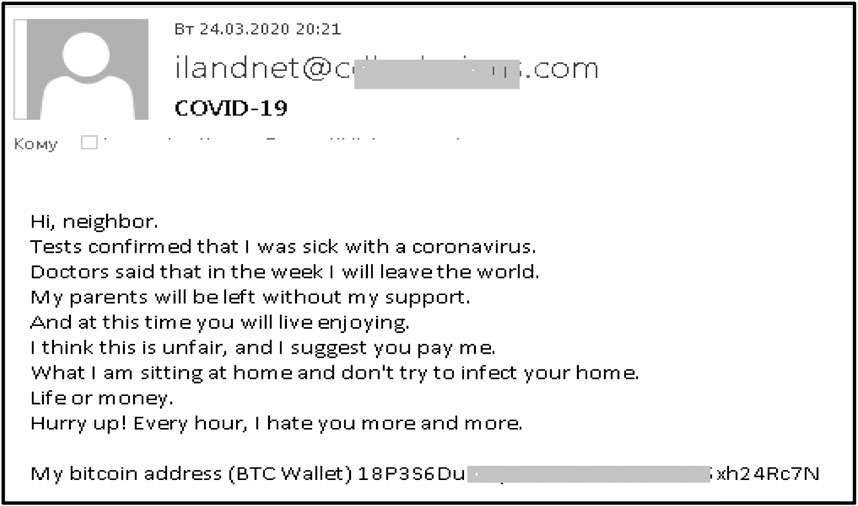
Frontiers Phishing Attacks: A Recent Comprehensive Study and a

PDF) Developing Anti Spyware System using Design Patterns

Security risks of global software development life cycle: Industry

FortiMail-100C - Fortinet

PDF) Head First Design Patterns

The threat from commercial cyber proliferation