Antivirus: The Ultimate Guide to Keeping Your Digital Assets Safe

Learn how antivirus software can protect your sensitive communication from various cyber threats and how to choose the right antivirus software for your needs.

What Is SOC 2: A Beginner's Guide To Compliance
Ultimate Guide to Cybersecurity: A Resource for Beginners

A Comprehensive guide to Penetration Testing: How to Protect Your
10 Ways to Secure Your Digital Life (2022 Updated)
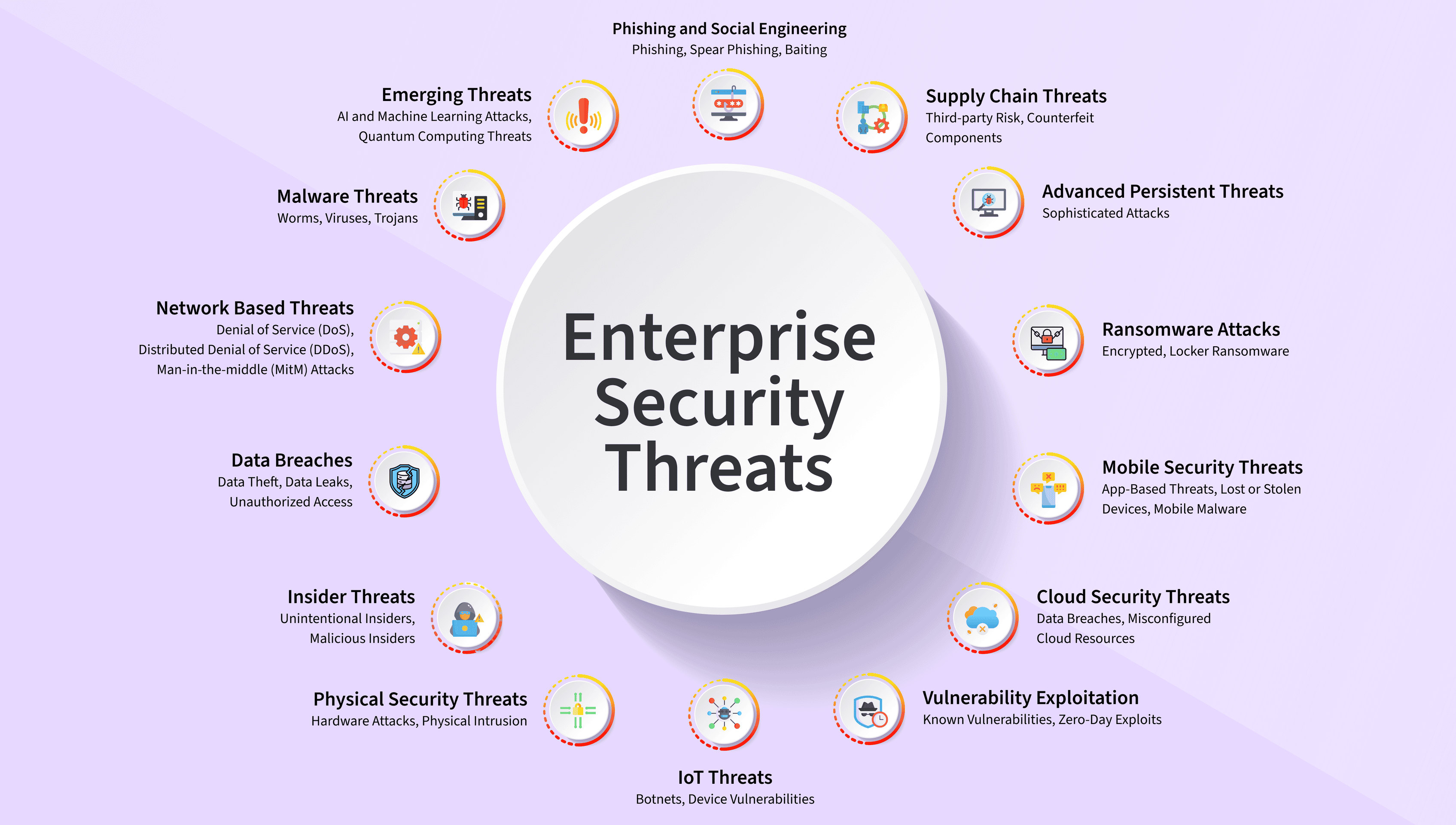
The Definitive Guide to Enterprise Security: Keeping Your Business

The Ultimate Guide to Cybersecurity: Protecting Your Digital World

Cyber Hygiene Best Practices For 2023 - ClearVPN

Protecting Your SMB: Traditional Antivirus vs. Next-Gen EDR vs. XDR

Fortify Your Online Business Security: Safeguarding Your Digital

Startup Survival Guide: Guarding Against Unauthorized Access and
-p-500%20(1).webp)
DivergeIT Cybersecurity: Your Guide to Cyber Security Practices