A Deep Dive into Windows Hello (2) - Hackers In inTrusion Laboratory
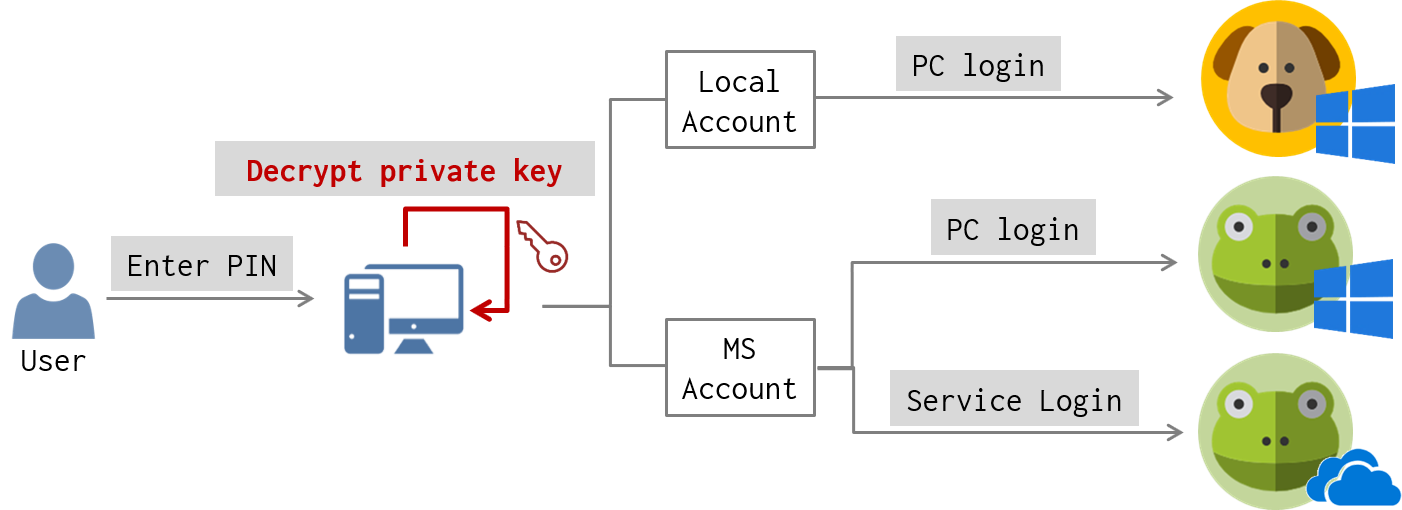
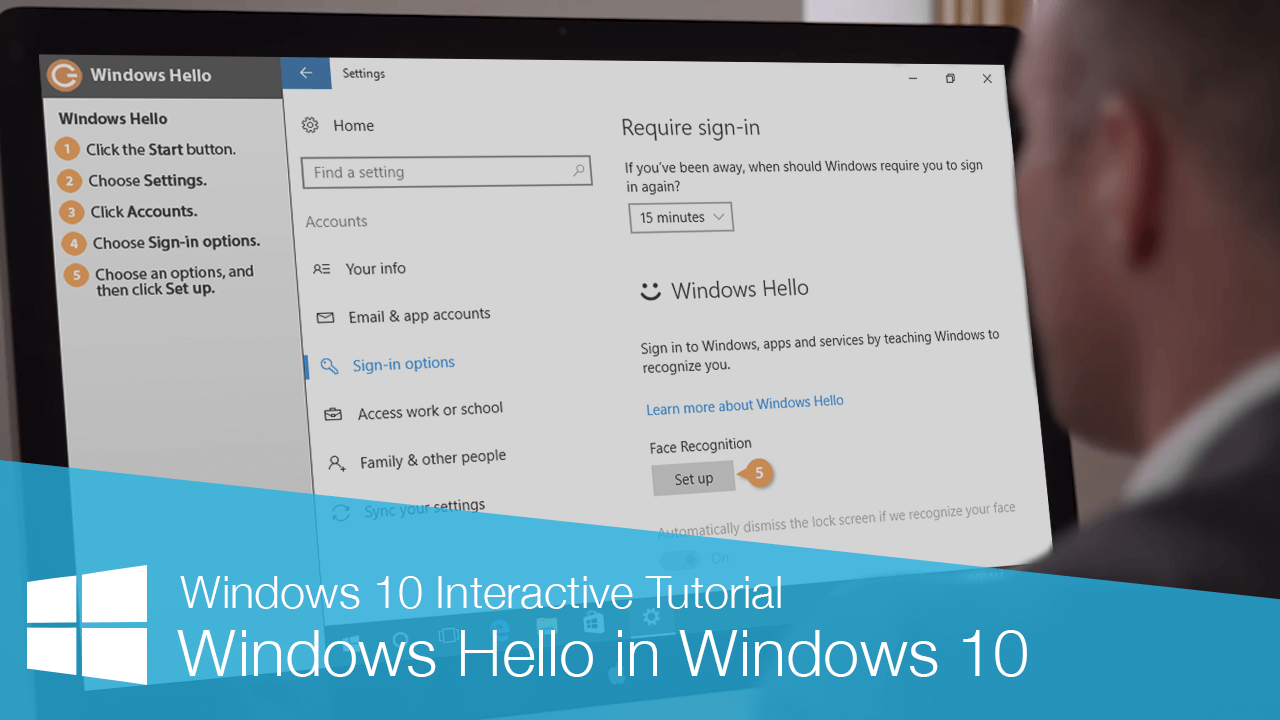
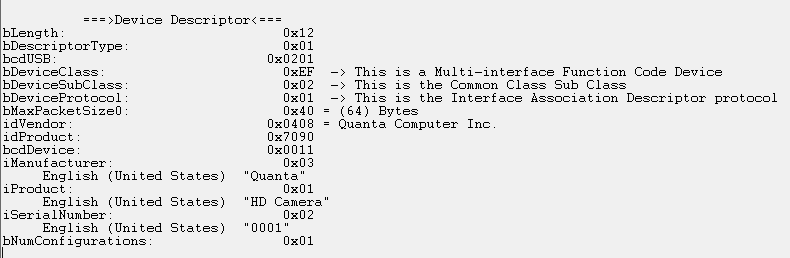
Client-side Login Procedures With protocol analysis, we figure out what data is exchanged between the client and the server for Windows Hello login. Now we’d like to know where is authentication data stored in the client-side? And how authentication data is used to? For these, we performed static and dynamic debugging for login-related services on … Continue reading A Deep Dive into Windows Hello (2) →
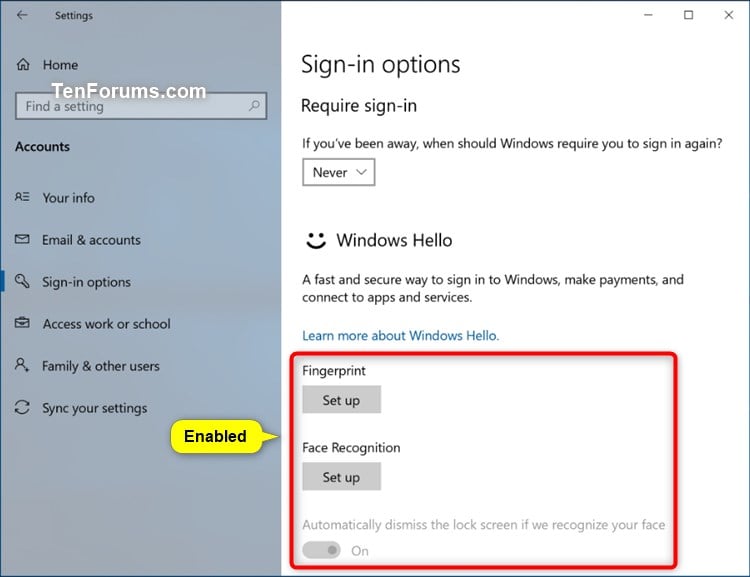
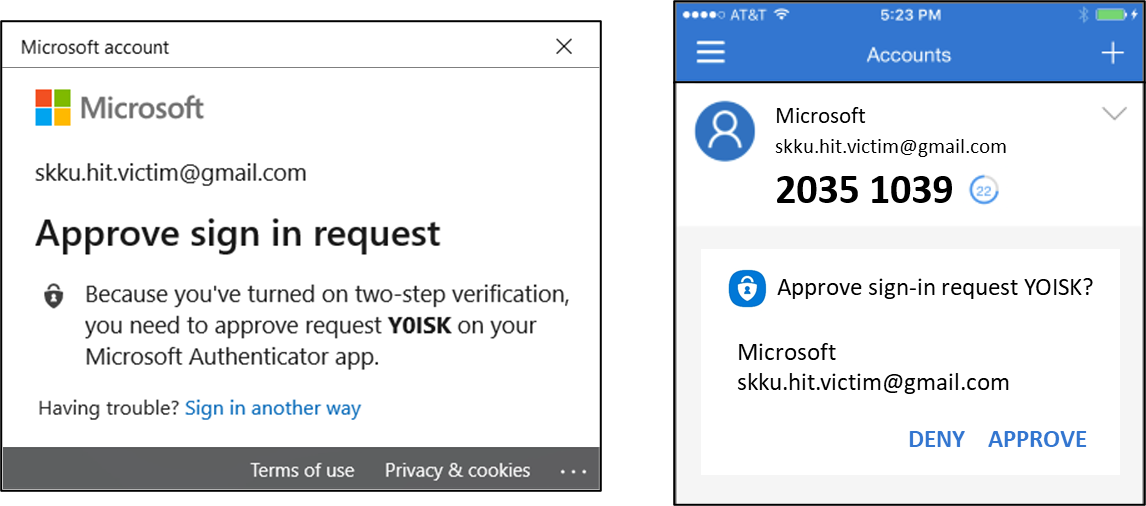
Bypassing Windows Hello Without Masks or Plastic Surgery

Gamee Hack Alert: $15M Gone in a Flash – What Happened? - Play to Earn Games News
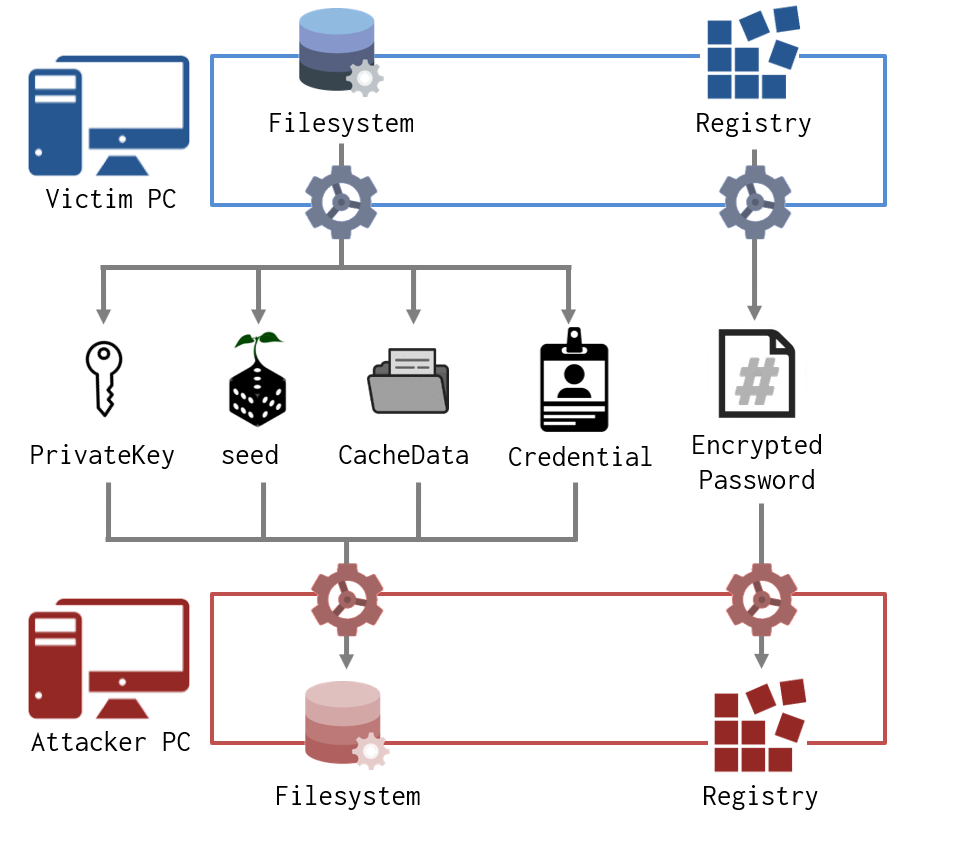
A Deep Dive into Windows Hello (2) - Hackers In inTrusion Laboratory
A Deep Dive into Windows Hello (2) - Hackers In inTrusion Laboratory

This Researcher Hacked Windows Hello Using the Ultimate in Public Data: Your Face

Blue Team Hacking Intrusion Detection with Snort

Bypassing Windows Hello Without Masks or Plastic Surgery

HPE SimpliVity Technical Deep Dive and Demo - Storcom, Lombard, Illinois, United States of America

MSAB Frontline Solutions - Forensic Focus
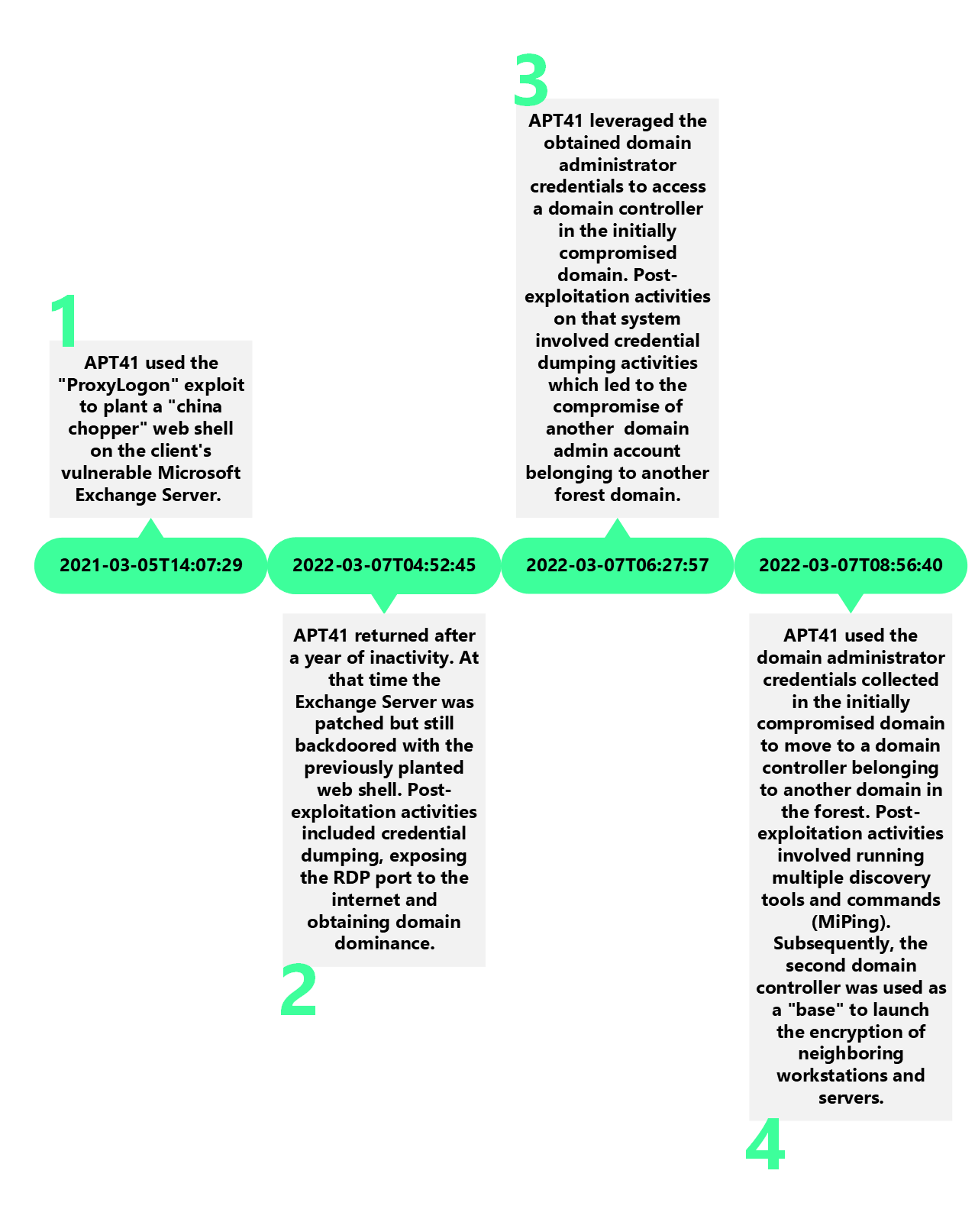
APT41 — The spy who failed to encrypt me, by DCSO CyTec Blog

Future Internet, Free Full-Text
Hacker techniques, exploit and incident handling

This Researcher Hacked Windows Hello Using the Ultimate in Public Data: Your Face